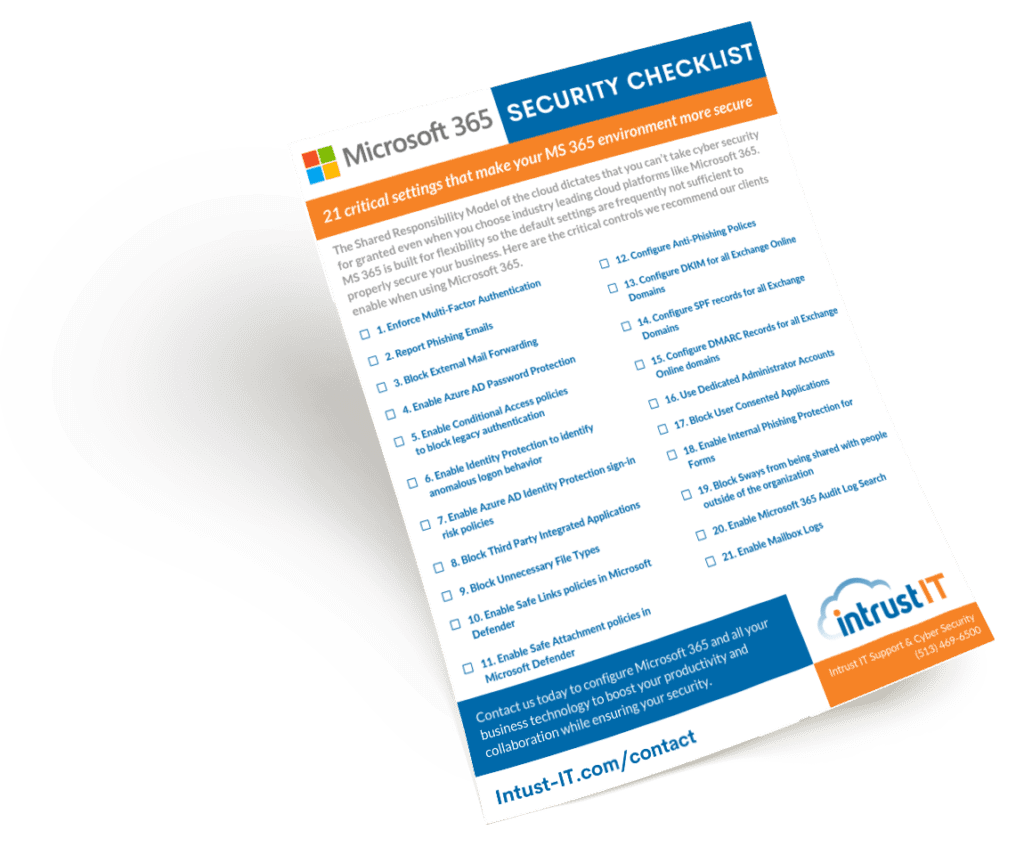
Downloadables (Checklists, Cheat Sheets & Guides)
Featured Videos
Explore the Latest Trends in IT
Why IT Companies Should Allow 9 Days Away From Keyboard
At Intrust IT, we understand how powerful recharging and rejuvenating are to our employees’ well-being. At the beginning of 2023,...
Exploit vs Vulnerability: What’s the Difference?
In cyber security, it's not uncommon to hear terms like "exploit," "vulnerability," "hacking" and "cracking" used interchangeably. But what is...

Considering IT Cyber Security? Are IT and Cyber Security the Same?
Businesses heavily rely on technology for their operations, and often, the terms "IT" and "cyber security" are used interchangeably. However,...
9 Days Away From Keyboard in Hawaii
At Intrust IT, we deeply appreciate the importance of recharging and rejuvenating. As we stepped into 2023, we made it...
Request a SCAP Compliant Vulnerability Assessment
Our advanced, non-invasive internal and external scans can identify security, performance and stability issues in your network. Get a preliminary scan followed by in-depth consultation with our technical and compliance specialists. After some time to consider the findings, we'll run another round of scans and consultations before providing the final report.