IT and Cyber Security Videos
Prefer to learn by watching? We have all your IT tips, recorded webinars, IT training and cyber security videos right here.
Tech Tips
About InTrust
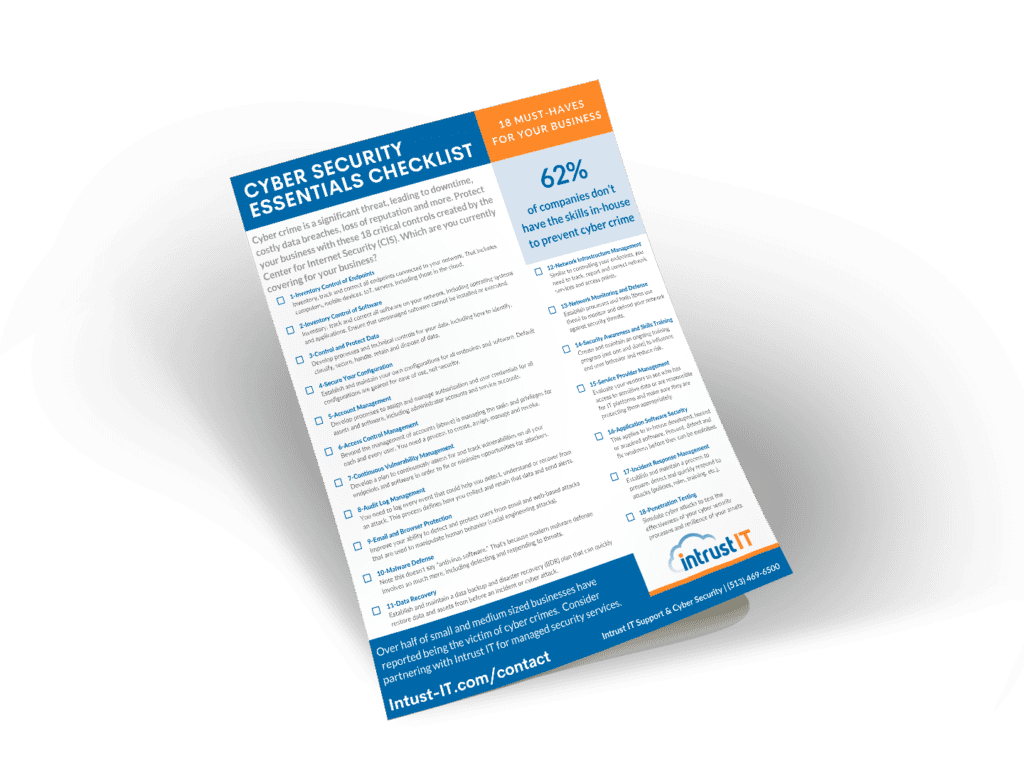
CIS Cyber Security Essentials Checklist
Does Your Cyber Security Measure Up?
Are you among the 62 percent of companies that don't having the skills in-house to prevent cyber crime? This easy to follow checklist can help. We summarized the 18 critical controls created by the Center for Internet Security (CIS) into this one page resource for businesses of all sizes. While there are many layers within each control, making sure your have the general category covered is a good start. Get the free download now.
Get the free checklist
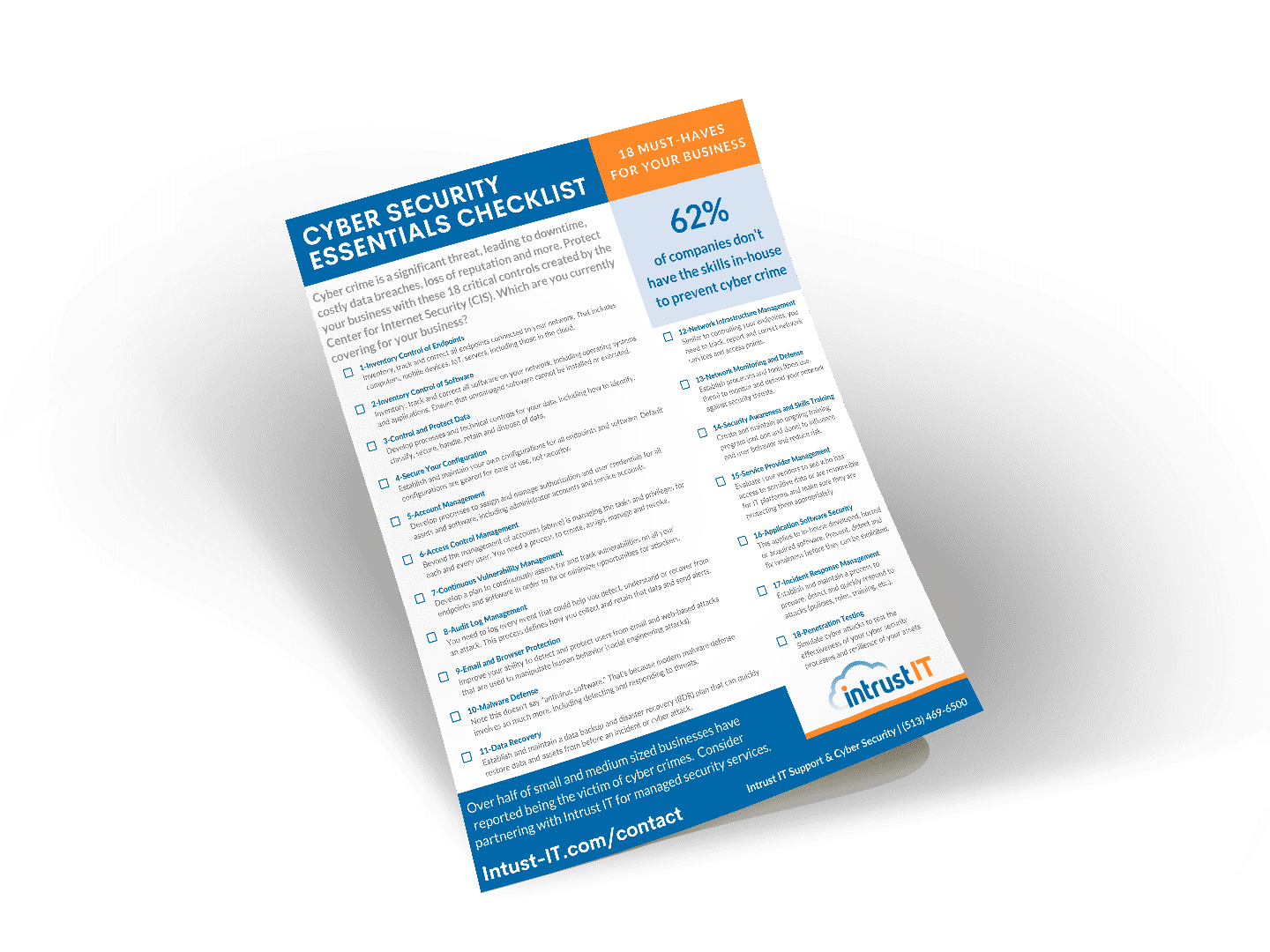
CIS Cyber Security Essentials Checklist
Does Your Cyber Security Measure Up?
Are you among the 62 percent of companies that don't having the skills in-house to prevent cyber crime? This easy to follow checklist can help. We summarized the 18 critical controls created by the Center for Internet Security (CIS) into this one page resource for businesses of all sizes. While there are many layers within each control, making sure your have the general category covered is a good start. Get the free download now.
Get the checklist
Explore the Latest Trends in IT

5 Cybersecurity Myths

Why Proactive IT Support Is a Must
Why IT Companies Should Allow 9 Days Away From Keyboard
Exploit vs Vulnerability: What’s the Difference?
Get Reliable IT Support
Get Reliable IT Support You Deserve Now
1. Schedule a time for us to meet (we'll come to you)
2. Tell us your tech troubles and ambitions
3. Partner with Intrust and get back to your goals
At your location, by Teams or phone