Social Media Security: If You Connect, Protect IT

So many of us connect to social media these days. Whether it’s to see photos of kids or grandkids who live on the other side of the country or it’s because we like to keep a pulse on health hints or even the latest jokes. But you might also be putting your cyber security at risk.
It is a jungle out there and even an innocent sentimental post such as, “Miss your deceased pets? Honor them here!” could be a ploy to get information about you that cyber criminals can use to gain access to systems and data.
It’s called social engineering — a trap set to trick you into sharing data. After all, pet names, street names or favorite actors/songs/movies — those are the things most passwords are made of.
Your social media pages are like catnip to criminals; furnishing them with a lot of information — especially when they cross reference it with all the other data you have shared on your other social media profiles. With your help. YOU give it to them.
Social Media Tricks To Avoid
These posts seem innocent. And the data doesn’t seem like anything critical. But here are just a few examples of social engineering posts.

Ever been tempted by a “ prove me wrong” puzzle like this one:
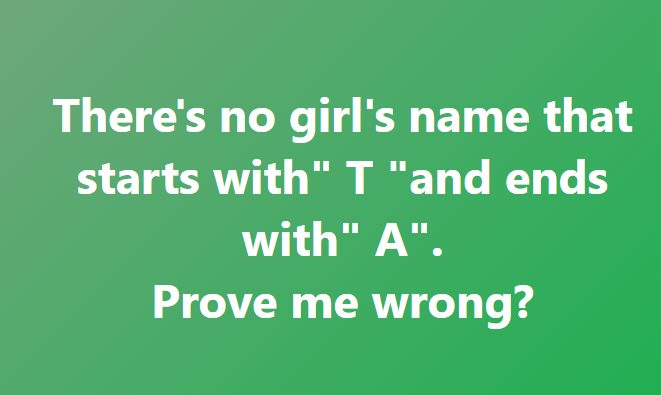
Though these brain teasers might be legit, they are most likely social engineering ploys.
How Bad Actors Use Your Social Media Data
It can work in a few different ways (and sometimes more than one), such as:
- You share info (like the pet’s name) and it’s used to answer a challenge question to gain access to your account. For the “What’s missing?” post, you just shared your favorite breakfast food (because it’s the one you noticed isn’t there… like bacon).
- The post itself links to a site that automatically downloads malware onto your computer. This can also happen with fake friend requests or even fake ads.
- Your data becomes part of a pool of data used in brute force attacks (more on that next).
You’re probably imagining a criminal searching through your social media and cross referencing that with every place you have an account, then typing in a bunch of challenges until they get in. While that’s certainly possible, criminals today don’t need to work nearly that hard. All they have to do is buy some software from the dark web. The software literally combs the internet millions of times a day, and scrapes data from all kinds of messages. It then dumps that info into a program that automatically challenges hundreds of accounts at a time until it gets in. These are called brute force attacks and criminals don’t even need to have hacking skills to run them. They just need to buy the software.
Tips to Improve Your Social Media Security
As a managed service provider, part of what Intrust does for clients is to provide ongoing cyber security training for the client’s entire team. That’s because social engineering and phishing are the easiest way for criminals to gain access to a network.
Training turns your biggest security risk (people) into human firewalls that know how to spot and resist falling for posts like these. Your employees are your best cyber security assets.
Here are some quick tips to help you get started:
- Protect all your devices. Whether you’re using a computer, smartphone or other network devices, all software needs to be updated regularly. Update to the latest security software, web browser and operating systems, as that is the safest protection against viruses and malware, and use anti-virus software.
- Limit the information you share on social media. Don’t include your address and other sensitive information or even a hint at your daily itinerary like your favorite coffee shop.
- Keep all specific information about you off social media. That includes but is not limited to your Social Security number, passwords, full name, address, birthday, even vacation plans.
- Turn off location services. Don’t put where you are or aren’t at any time on social media. If you want to share that you went to Disney World, post it AFTER you get home, not while you’re there.
- Let your friends know if they’ve shared something about you that makes you uncomfortable or you think is inappropriate. By all means, allow them to speak up if you’ve done that to them.
- Report all incidents of suspicious or harassing activity. Most social media platforms want reports like this so that they can block harassing users. If you’ve been a victim of cybercrime, let local and national authorities know. They are ready to help you.
- Remember there is no “DELETE” on social media. Even if you delete a post or picture within seconds, chances are someone already saw it and it is still on a backup server or archive somewhere. Consider that when you post. The speed of lightning is nothing compared to the speed of the internet.
- Update your security settings. Set the security and privacy levels for information sharing at a comfortable level.
- Disable geotagging on social media. Geotagging a website, photo or other data with your specific location (latitude and longitude) allows anyone to see where you are—and where you are not—at any given time.
- Connect only with people you trust. While some social networks might seem safe because of the limited personal information you share through them, keep your connections to people you personally know and trust.
Share this Blog

Is Your Name or Birthday a Part of Your Password?
If so, you’re a part of the 59 percent of people who don’t follow proper password hygiene. More than 70 percent of passwords are used for more than one system, meaning if cybercriminals crack one, they can access a lot more accounts.
Our free Enterprise Password Management Guide will give you the best password hygiene practices to help you secure your computer and your business.
Download the Guide
Explore the Latest Trends in IT
Redefining Culture in IT Companies: Nine Days Away on an American River Cruise

Was Your SSN Leaked? Understanding the Impact of a National Public Data Breach

What Are Managed IT Services? A Simple Guide