Local Government Security Breaches: Are City Officials Prepared?

Virtually every day there’s a new headline about novel cyber threats, government security breaches and municipal government cyber attacks that lead to theft of money, theft of data, and critical outages.
While it’s tempting to bury your head in the sand, thinking “This will never happen to us,” we can tell you from decades of first hand experience that hope and denial are not a good strategy. Local governments are firmly in the crosshairs of bad actors of all types.
Because successful cyber attacks often yield large payouts for cyber criminals and adversarial governments, you can all but guarantee that cyber attacks will be an ongoing issue for years to come as our society becomes increasingly digital and we rely more on technology for work, commerce, education and entertainment.
As hackers’ tools and techniques improve, agencies that fail to prepare for cyber attacks are preparing to fail both their citizens and their employees.
For example, FBI Director Christopher Wray has warned about Chinese government attacks targeting critical infrastructure such as water plants and 911 systems among others. You can learn more about Wray’s recent congressional testimony in this article from Reuters: “US officials deliver warning that Chinese hackers are targeting infrastructure”.
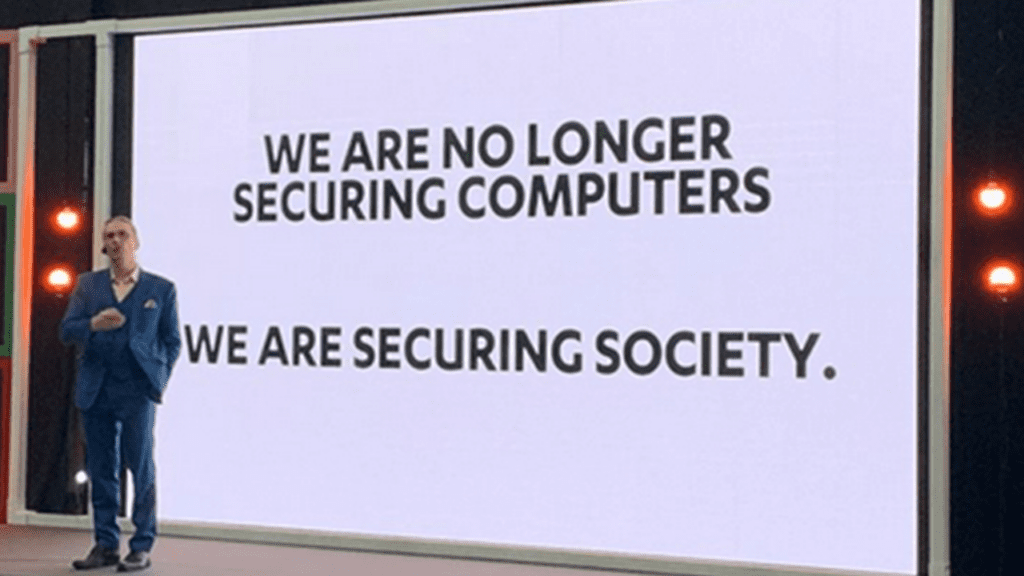
Former NSA Director General, Paul Nakasone, said “Cybersecurity is national security,” and we completely agree. As an expert managed service provider with more than three decades of experience in keeping our clients stable, productive, AND secure, we want to help your municipal agency defend against cyber attacks and recover quickly should one succeed.
Local Spotlight: The Huber Heights Cyber Attack
Are you aware that over 70 percent of all ransomware attacks are targeted toward municipal and county governments?
Unfortunately, Huber Heights recently faced the harsh reality of a cyber attack that took down multiple government systems and functions. Three weeks after the attack, officials were still grappling with the aftermath and facing uncertainties about the hackers’ release of residents’ and employees’ personal data.
The ransomware gang, BlackSuit, claims to have released a 129-GB file of the city’s data. At the time of this writing, the status of Huber Heights data remains unknown, but a common tactic now employed by hackers is to publicly release stolen information to create additional leverage for the payment of a ransom.
City Manager, Rick Dzik, acknowledges the challenges, stating, “It took a long time to download information from the dark web to determine what personal information, if any, was obtained by the threat actors.” The city is actively reviewing the released data with the assistance of forensic investigators.
Dzik said that an affirmative vote from the city council gave him the authority to use up to $350,000 in city funds to respond to the cyber attack. He noted the city’s cyber security insurance will cover a portion of the costs.
The bottom line?
Your town or city can’t afford to suffer a ransomware attack. Here are 11 concrete steps you can take today to secure your local government’s systems.
1. Leverage Federal Resources to Harden Digital Infrastructure
The federal government has approved billions in grants for local governments to improve their digital infrastructure via the American Rescue Plan Act and the Infrastructure Investment and Jobs Act.
Both acts grant local governments the ability to allocate funds for preventing city cyber attacks by improving broadband infrastructure, arming against government hacking tools and embracing cloud-based software.
You should also explore The Multi-State Information Sharing and Analysis Center (MS-ISAC) which is a CISA-supported collaboration with the Center for Internet Security designed to serve as the central cybersecurity resource for the nation’s State, Local, Territorial, Tribal (SLTT) governments. The MS-ISAC is a membership-based collaborative that is open to SLTT entities of all types, including SLTT government agencies, law enforcement, educational institutions, public utilities and transportation authorities.
MS-ISAC members receive direct access to a suite of services and informational products including cybersecurity advisories and alerts, vulnerability assessments, incident response support, secure information sharing, tabletop exercises, a weekly malicious domains/IP report, and more.
2. Double Down on Your Local Government IT Department
While great government technology workers are crucial for managing and securing your agency’s information technology systems, recruiting and retaining qualified technology staff can be difficult. One way to address the skills gap is to leverage the skills and expertise of Managed Service Providers (MSPs). You can work with an MSP to fully outsource your IT support and cybersecurity protection needs or to augment your current team.
Additionally, having an organized IT ticketing strategy ensures that bugs in the system and potential cyber security threats don’t go unnoticed.
With government management software, IT ticketing becomes an automated process. Tech issues from other government departments are automatically timestamped and added to the government IT ticketing software module for easy access.
3. Implement Multi-Factor Authentication (MFA)
Multi-factor authentication (MFA) aka Two-Factor Authentication (2FA) or Two-Step Verification adds an extra layer of security by requiring users to provide multiple forms of identification before accessing systems or data. MFA significantly reduces the risk of unauthorized access, even if passwords are compromised.
MFA is not a silver bullet, but it raises the bar for bad actors, many of whom will move on to softer targets. You should implement MFA on all systems that support it and consider replacing those that don’t.
4. Migrate From Physical On-site Servers
Physical on-site servers are prime targets for a city cyber attack. They are also expensive to manage and maintain, especially for small to mid-sized local governments.
Cloud-based solutions such as SharePoint in Microsoft 365 can reduce costs and reduce the risk of permanent data loss. Cloud providers also push system updates and upgrades regularly, ensuring that your data is secure and your team is productive.
5. Encrypt Sensitive Data
Encrypting sensitive data adds an extra layer of protection, making it unreadable to unauthorized users. City officials should ensure that all sensitive information, both in transit and at rest, is encrypted to safeguard against potential data breaches.
6. Secure Mobile Devices and Remote Access
Given the rise in remote work, securing mobile devices and managing remote access is vital. Implement policies and tools to secure smartphones, tablets and laptops used by government employees, ensuring that sensitive data remains protected, even outside the traditional office environment.
For example, ensure that all data on remote devices is encrypted.
7. Require Regular Cyber Security Training
Phishing scams affect people who are caught off guard, every single day. Sadly, they are becoming increasingly sophisticated due to AI deepfake technology. For example:
Deepfake scammer walks off with $25 million in first-of-its-kind AI heist
Government employees who use weak passwords make it easy for hackers to break into local government systems with minimal effort.
To prevent embarrassing and expensive cyber attacks, provide regular cyber security training that helps your users learn how to identify and avoid these attacks.
Check out our free cybercrime prevention guide and password management guide for more cyber security tips and insights into strengthening your passwords.
8. Conduct Regular Cyber Security Vulnerability Assessments
You can identify security, stability and performance issues by scheduling a cyber security vulnerability assessment. At Intrust IT, we use advanced, non-invasive, security content automation protocol (SCAP) compliant vulnerability assessment tools to perform an internal and external scan of your environment.
As a result, you will receive:
- A preliminary report detailing areas of concern.
- A second scan and interview after you’ve had a chance to digest the preliminary report.
- A final report that includes all items discovered along with detailed scan data.
- An in-depth consultation and interview with certified cybersecurity experts to determine compliance with the Center for Internet Security (CIS) Critical Controls.
9. Establish an Incident Response Plan
It is critical to have a well-defined and tested Incident Response Plan (IRP) in the event of a cyber attack. City managers should ensure that their teams are trained on response procedures, including communication strategies, containment measures and recovery steps.
10. Establish a Business Continuity Plan
It is also critical to have a well-defined and tested Business Continuity Plan (BCP) because it can help you minimize downtime and costs, and recover quickly in the event of a successful attack.
11. Foster a Culture of Cyber Security Awareness
Encourage a culture of cyber security awareness among government employees. Regularly communicate the importance of following security protocols, recognizing potential threats, and reporting suspicious activity.
Ensure that staff members understand they are encouraged to question and report suspicious behavior and should err on the side of caution.
An informed, vigilant, and supported workforce is a crucial line of defense against cyber attacks
Next Steps: Equip Yourself With Additional Cyber Security Knowledge
The Huber Heights cyber attack serves as one of many stark reminders of the growing threats faced by local governments. City officials can significantly reduce the risk of local government attacks by implementing these cyber security tips.
If you want to learn more about preventing security breaches in local government, contact us or schedule a no-obligation consultation with our certified cybersecurity experts today.
Share this Blog

Is Your Name or Birthday a Part of Your Password?
If so, you’re a part of the 59 percent of people who don’t follow proper password hygiene. More than 70 percent of passwords are used for more than one system, meaning if cybercriminals crack one, they can access a lot more accounts.
Our free Enterprise Password Management Guide will give you the best password hygiene practices to help you secure your computer and your business.
Download the Guide
Explore the Latest Trends in IT

Securing Our Cities: Cybersecurity Protection for Local Governments

Manufacturing and IoT: Securing Connected Devices

Small Business Cyber Security Toolkit: The Tools You Need to Stay Protected




