Starting With a Managed IT Services Provider: What To Expect the First 45 Days

First of all, don’t expect solutions immediately. You’ll get them, but first, all IT companies will want to chat with you and discover exactly what you need and where their company can provide solutions. And realize that not all IT providers provide the same services and the same level of security. If you are in the process of vetting possible MSPs, download our free Managed IT Support Checklist to help you compare.
The First Meetings With an IT Services Provider
When you contact us at Intrust IT, we start with a discovery interview. This is usually a 30-minute phone call during which we briefly discuss your business needs and our services to determine if there’s a good fit between us.
If there’s a fit, the next step is the first in-person appointment. We will want your lead engineer and your account manager to be present, as well as any other staff who are critical to helping us develop a plan. We will need to address how reliant your business is on IT technology, including:
- What technology you currently have, what your immediate goals are, and what they are for the future.
- Your current number of endpoint devices (computers, smartphones, etc.) and whether they are located on-site or are remote.
- Whether you are currently using an on-site server or a cloud-based one. We recommend cloud-based for several reasons that can be discussed during this process.
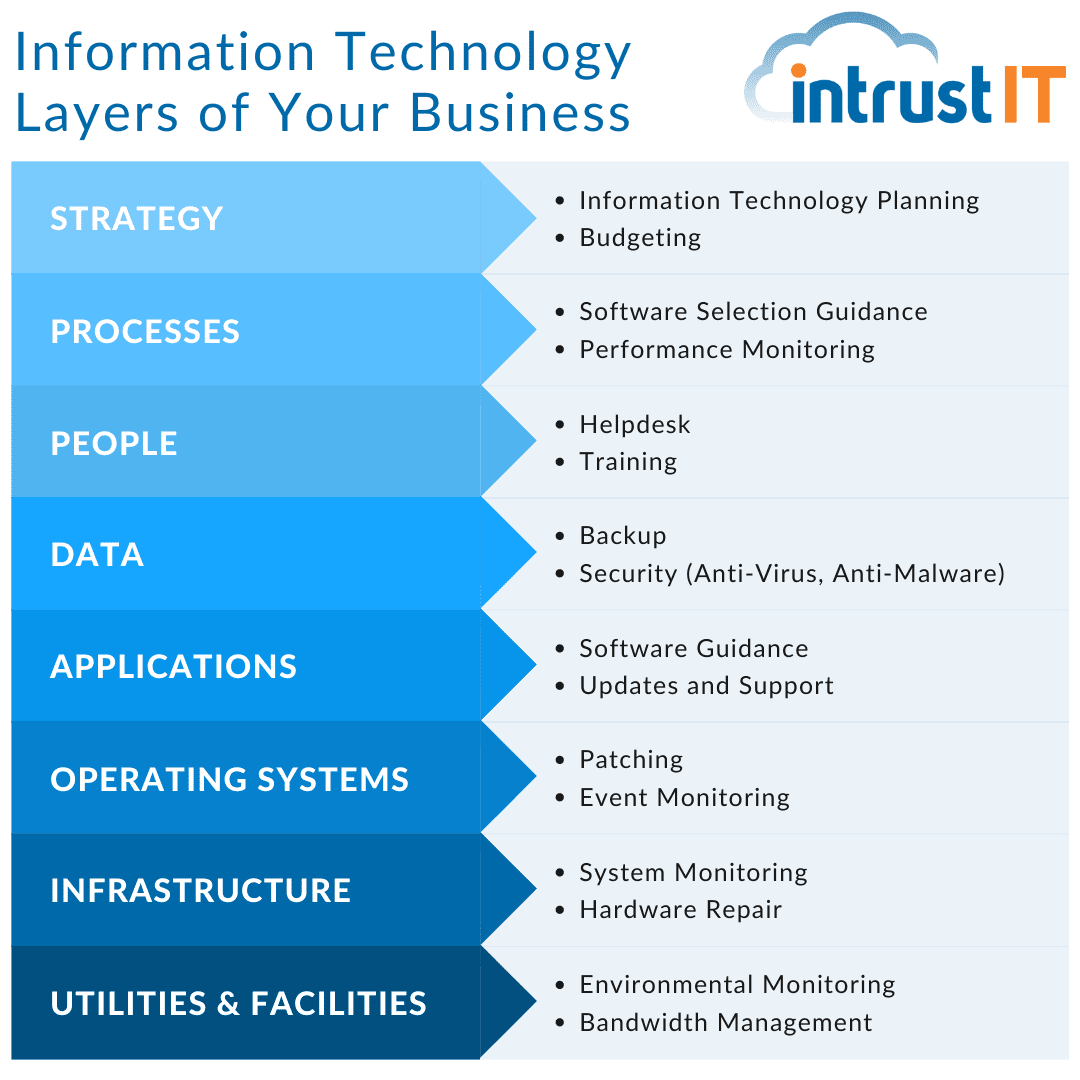
Over the 25 years Intrust IT has been in the technology business, we have developed eight information technology layers that represent the reliance of businesses on IT. Starting at the bottom, each layer relies on all the underlying layers in order to support its operation. It’s a good format to use when interviewing other IT providers and comparing them to us.
Once they determine your needs, prospective providers will develop a plan and present it for review.
The Kick-Off
The process of getting your business up and running with all our services is called onboarding and it starts with a kick-off. This process includes a full review of your master service agreement to make sure everyone knows what to expect from the services, process and timeline. Once the agreement is signed, onboarding begins.
Onboarding With Your IT Services Provider
The onboarding process will begin on the first of the month after the contract has been signed. Onboarding takes a minimum of two weeks. It can be done faster, but experience at Intrust has taught us that it’s best not to rush. We want to make sure we get everything right from the start.
The first part of onboarding is documenting what is currently in place. Then we’ll start adding on the suite of security, endpoint management and backup tools that we use to manage your technology needs. This process takes the bulk of the onboarding time because it means touching every device on your network. It may seem a little quiet to you as this process rolls out, but the Intrust IT team will be making sure every single device is ready to begin living under Intrust’s umbrella of service and protection.
This also is an opportunity for us to create a lifecycle plan to help you stay ahead of any IT purchase needs. This initial budgeting guide will be updated quarterly for as long as Intrust serves as your managed service provider (MSP).
Intrust onboarding specialists and the account manager will work with their staff of 10 technicians and eight engineers to complete all necessary tasks.
Pre-Launch Training
Just prior to the going live date, Intrust IT provides training to your staff that includes two key components: how to get IT help when they need it and general cyber security awareness.
For the IT system training, staff will learn
- How to report a problem.
- The levels of priority to establish and examples
- What response time frame to expect for each priority level
While each client can customize the priority levels and response times in their agreements, Intrust usually responds to urgent issues immediately and non-urgent in about an hour.
Cyber security training is critical because a criminal’s easiest way into your system is to trick someone who already has access to it. Our cyber security awareness training helps your team understand the risks, spot common ploys and report anything suspect.
Launching With an IT Services Provider
This is the point when we “switch on” Intrust IT support for your company. Your endpoints are monitored and protected, we’re proactively addressing issues and your team knows how to reach us for help and what to expect when they do.
The first month may have some speed bumps – issues that weren’t uncovered during onboarding that need to be addressed or some “getting comfortable” time for both teams. With ongoing and open communication, we’ll work through these together and make sure there is as little impact on your business as possible.
Ongoing Support With an IT Services Provider
At Intrust IT, we offer proactive IT support. That means we don’t just wait for you to tell us there’s a problem. We actively monitor your systems, analyze your usage patterns and advise you on ways to get the most out of your technology.
We’ll have regularly scheduled meetings, often weekly, but sometimes more or less often depending on each client’s preferences.
Going with a new or a new-to-you IT provider can feel daunting. We hope these insights will make it a little easier, no matter which IT provider you choose. Of course, we hope you’ll consider Intrust IT. Please feel free to contact us or book a meeting to talk through your technology needs.
Share this Blog

Is Your Name or Birthday a Part of Your Password?
If so, you’re a part of the 59 percent of people who don’t follow proper password hygiene. More than 70 percent of passwords are used for more than one system, meaning if cybercriminals crack one, they can access a lot more accounts.
Our free Enterprise Password Management Guide will give you the best password hygiene practices to help you secure your computer and your business.
Download the Guide
Explore the Latest Trends in IT

Securing Our Cities: Cybersecurity Protection for Local Governments

Manufacturing and IoT: Securing Connected Devices

Small Business Cyber Security Toolkit: The Tools You Need to Stay Protected




