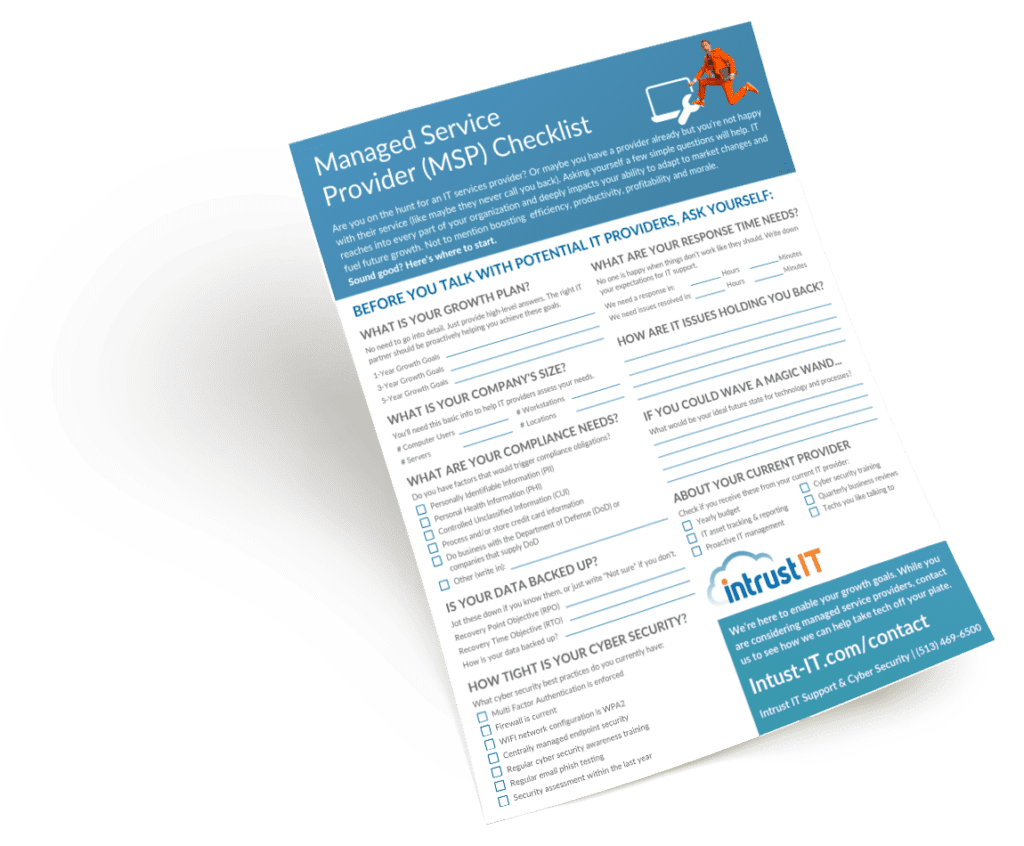
Downloadables (Checklists, Cheat Sheets & Guides)
Featured Videos
Explore the Latest Trends in IT

Microsoft 365 vs Google Workspace: Which Is Right For Your Organization?
Who wins the Microsoft 365 vs Google Workspace smackdown? Like many other decisions, the answer depends … on the size...

How To Stop Unwanted Emails
We all receive those pesky spam emails that crowd your inbox and make it difficult to organize. They can be...

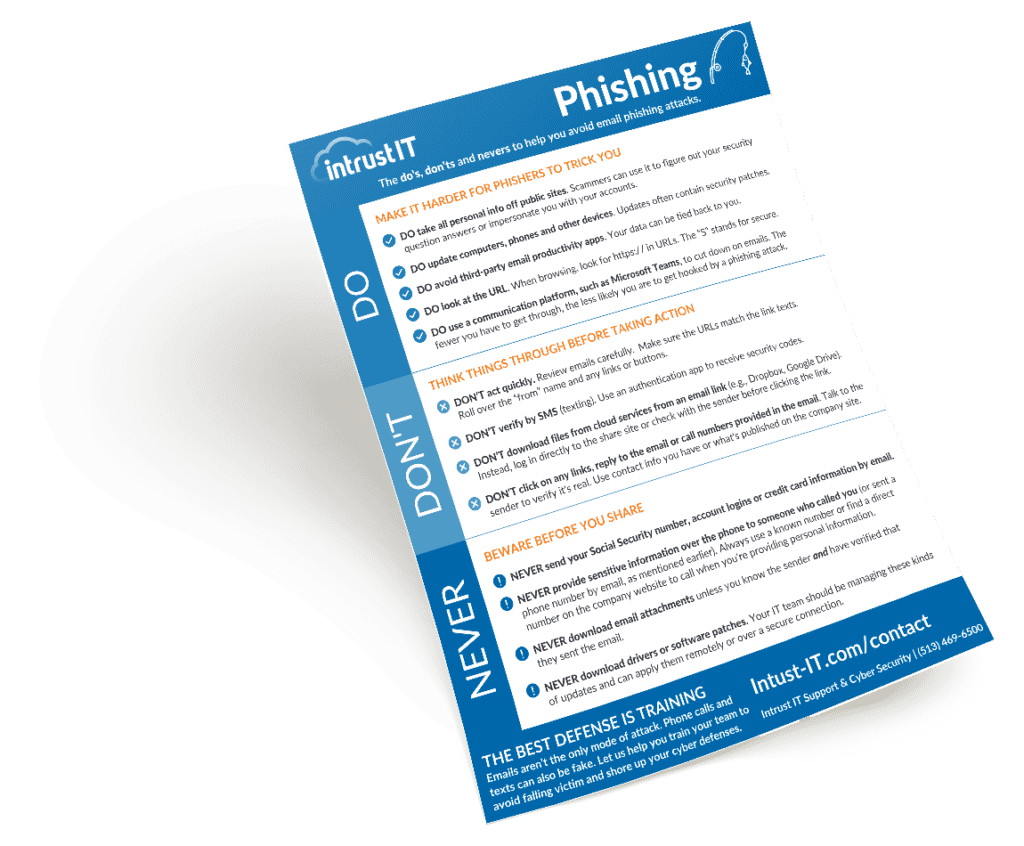
Prevent Phishing With The SLAM Technique
Phishing has become the top method cyber criminals use to attack companies, whether that’s hitting them with ransomware, breaching their...
Insider Threat Indicators and Prevention Tips
We often think of cyber threats as coming from outside our company, or even from other countries — and that...
Request a SCAP Compliant Vulnerability Assessment
Our advanced, non-invasive internal and external scans can identify security, performance and stability issues in your network. Get a preliminary scan followed by in-depth consultation with our technical and compliance specialists. After some time to consider the findings, we'll run another round of scans and consultations before providing the final report.