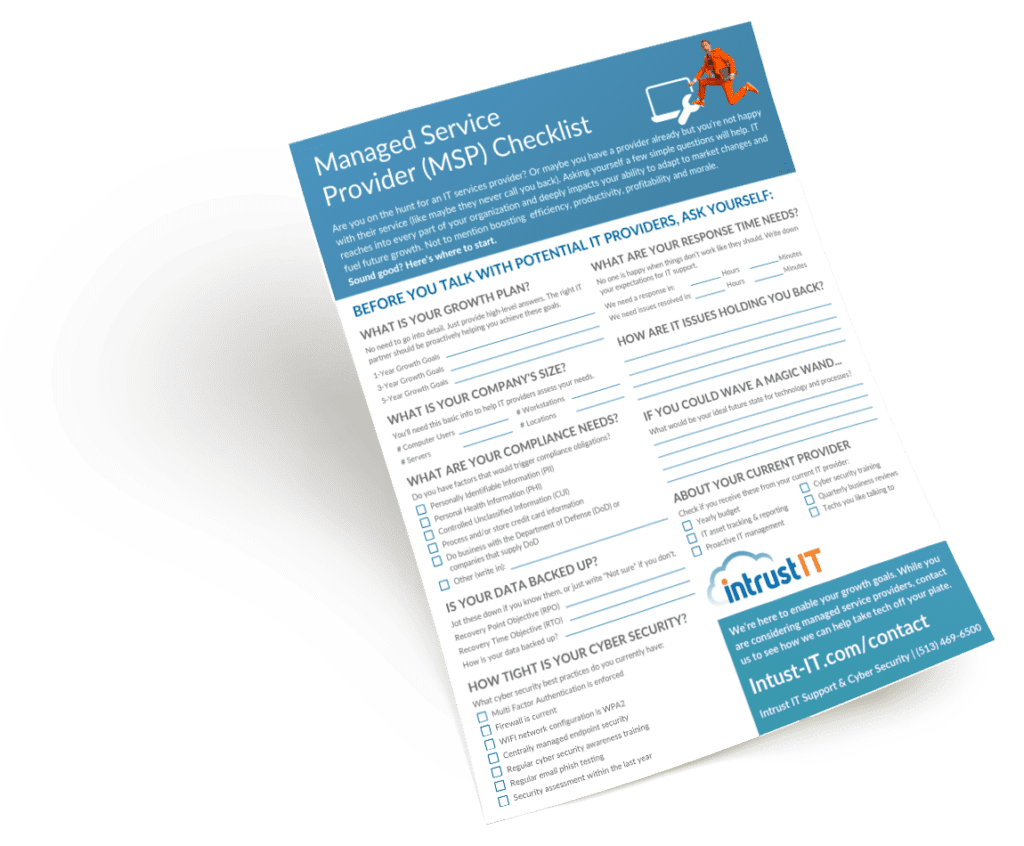
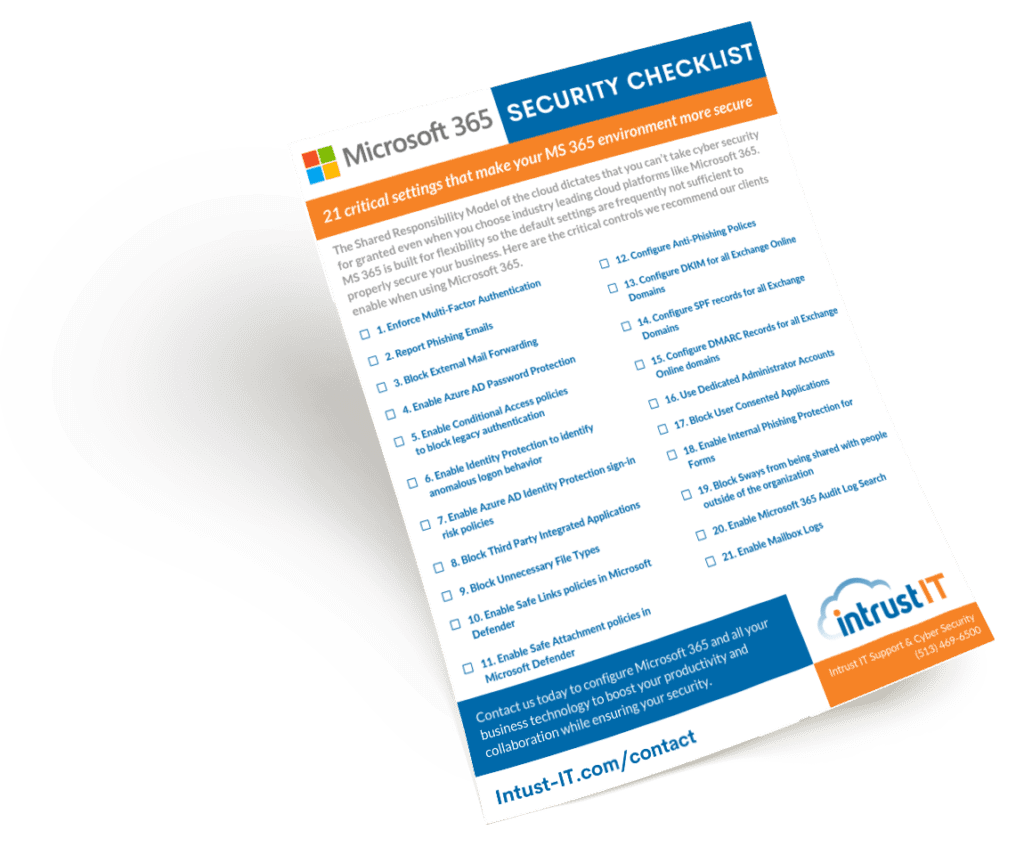
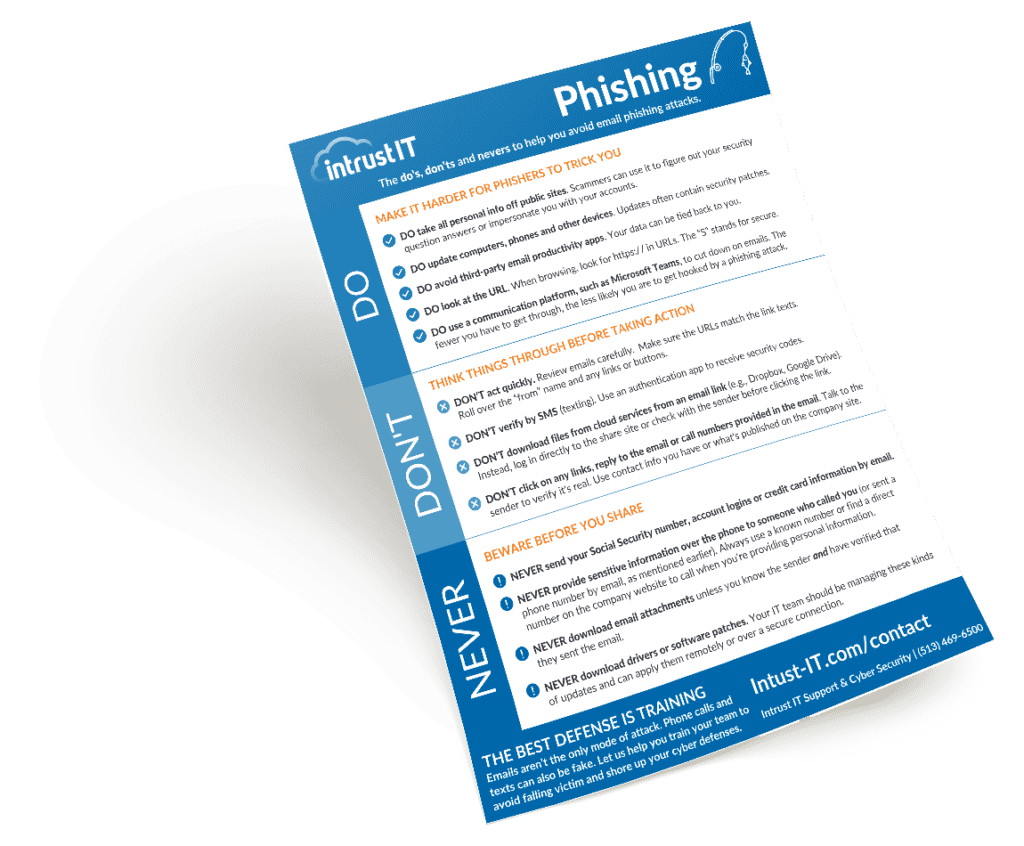
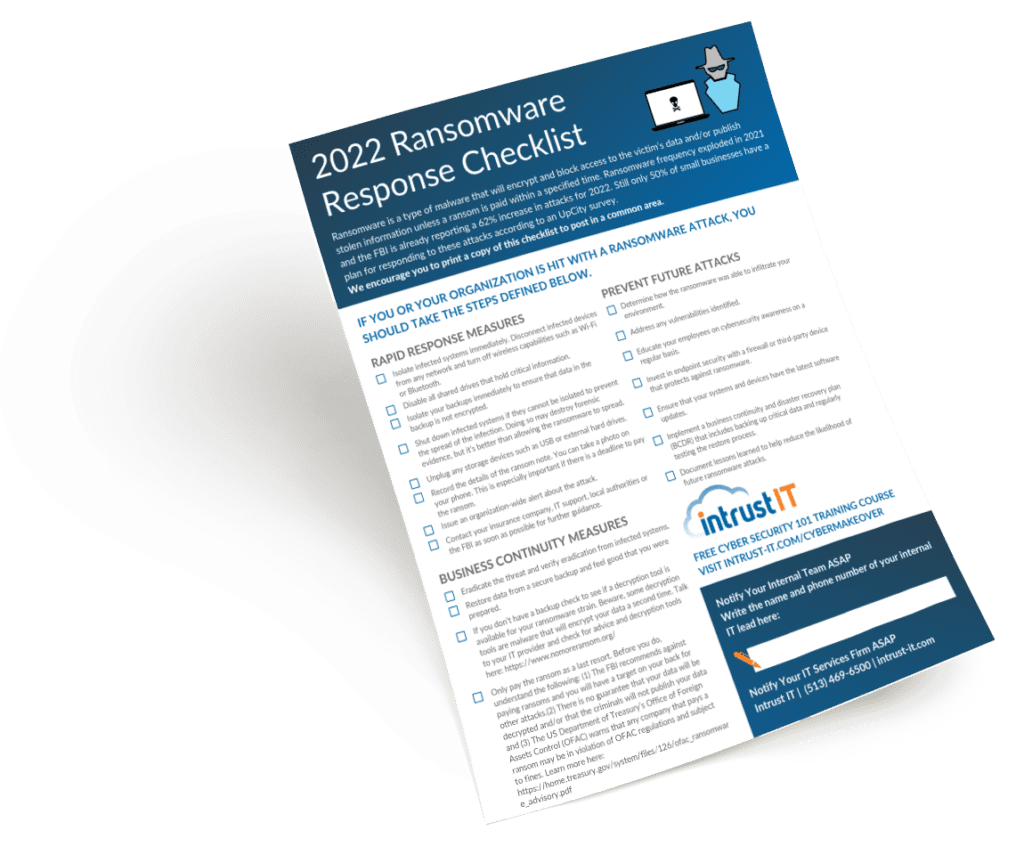
Downloadables (Checklists, Cheat Sheets & Guides)
Featured Videos
Explore the Latest Trends in IT

Cyber Attacks Are Rising, New Cyber Security Legislation
The latest statistics from the Federal Bureau of Investigation (FBI) demonstrate that no industry is exempt from cyber attacks which...
A Leader’s Guide to Creating a Foolproof Business Continuity Plan (and Why It’s Important)
Are you ready for a crisis? Fire, flood, breach, ransom? If your business has been running smoothly, you might think...

What Is a VCISO and What’s the Benefit For Your Company?
Have you noticed your IT team wearing too many hats and stretched way too thin lately? Asking them to be...

Tech Tip Video #1: How to Send an Encrypted Email in Microsoft 365
Today, we're going to be showing you how to send an encrypted email. The reasons you might want to encrypt...
Request a SCAP Compliant Vulnerability Assessment
Our advanced, non-invasive internal and external scans can identify security, performance and stability issues in your network. Get a preliminary scan followed by in-depth consultation with our technical and compliance specialists. After some time to consider the findings, we'll run another round of scans and consultations before providing the final report.