Downloadables (Checklists, Cheat Sheets & Guides)
Featured Videos
Explore the Latest Trends in IT

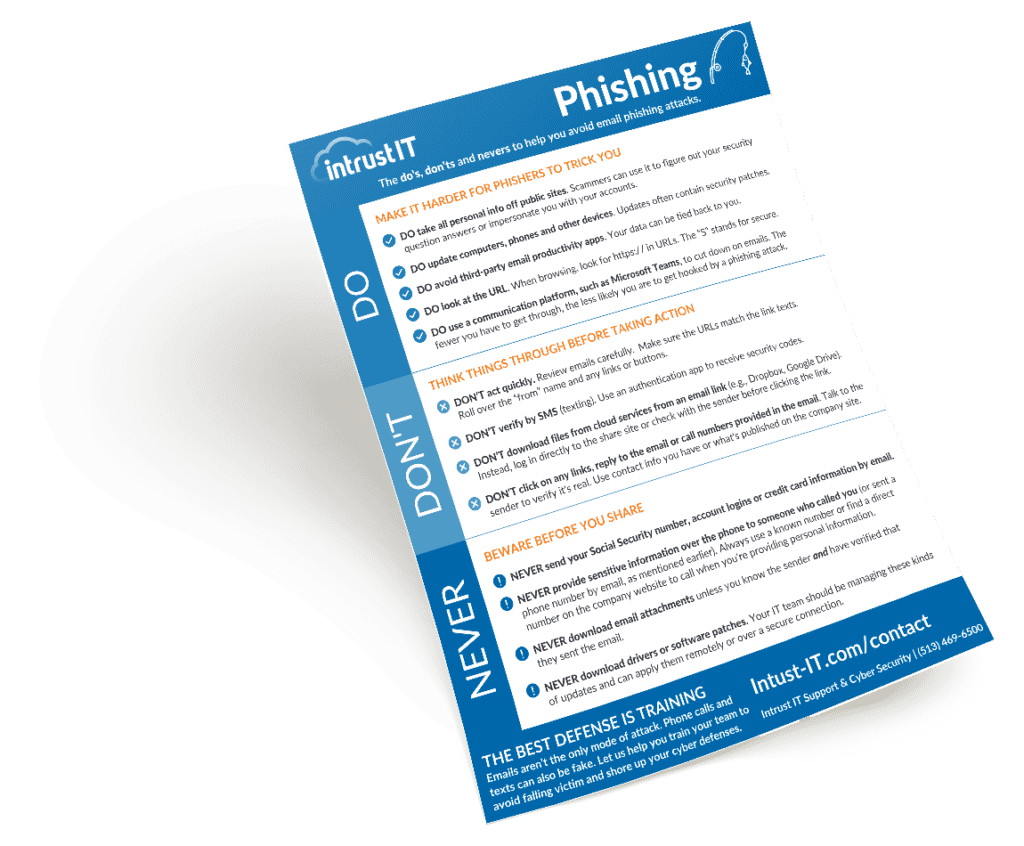
Best Practices to Prevent Phishing Attacks
No cybersecurity techniques can prevent phishing or other types of cyber attacks if the end user doesn’t know best how...
Email Security Trends and Preventing Email-Borne Cyber Attacks
There’s a good reason we talk about email security trends a lot in this blog and with our managed IT...

Intrust IT of Cincinnati Named a 2022 All-Star Company by The Great Game of Business®
Cincinnati, OH: The Great Game of Business, Inc. congratulates Intrust IT for being named as a 2022 Great Game of...

7 Business Cyber Security Tips for the Holidays
The holidays are a time of giving, but for hackers, it's a prime opportunity to steal data and money. Companies...
Request a SCAP Compliant Vulnerability Assessment
Our advanced, non-invasive internal and external scans can identify security, performance and stability issues in your network. Get a preliminary scan followed by in-depth consultation with our technical and compliance specialists. After some time to consider the findings, we'll run another round of scans and consultations before providing the final report.