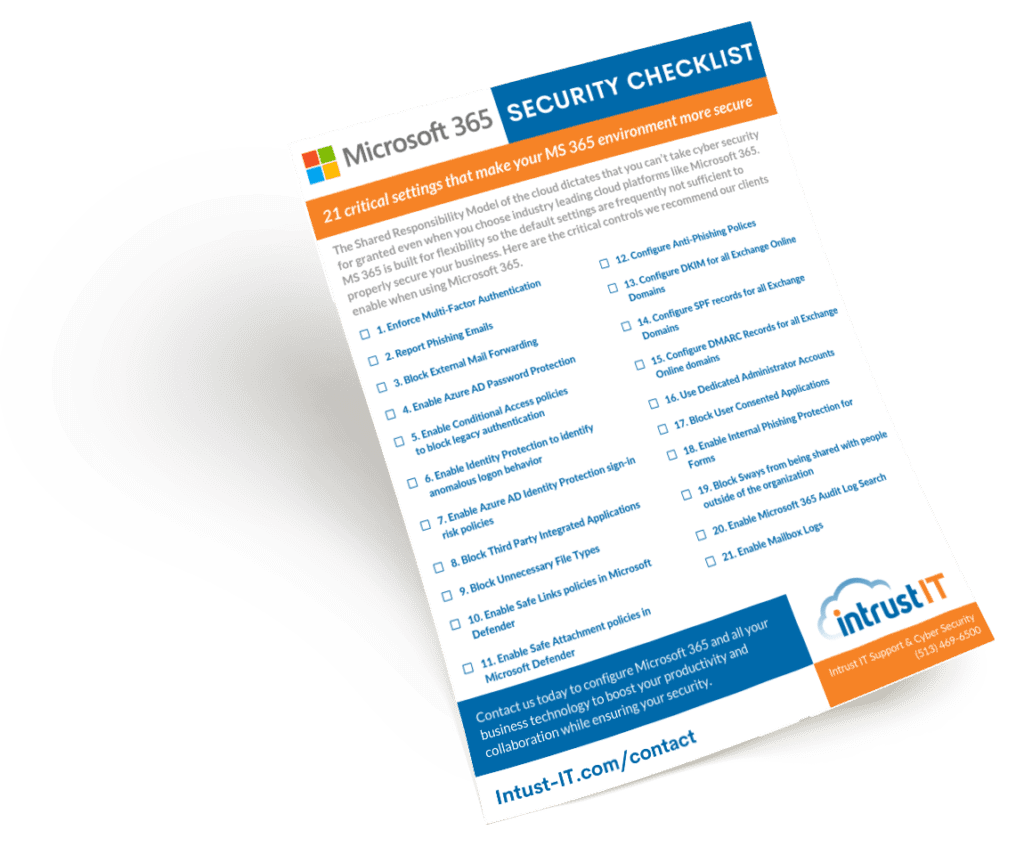
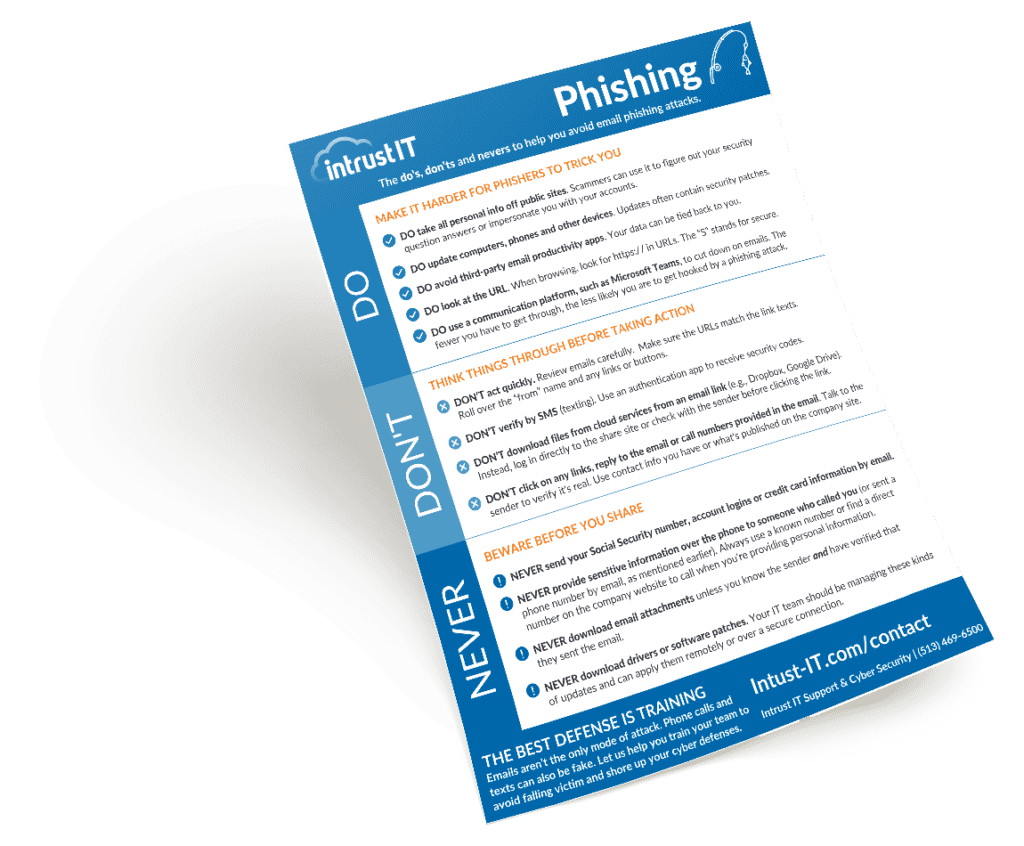
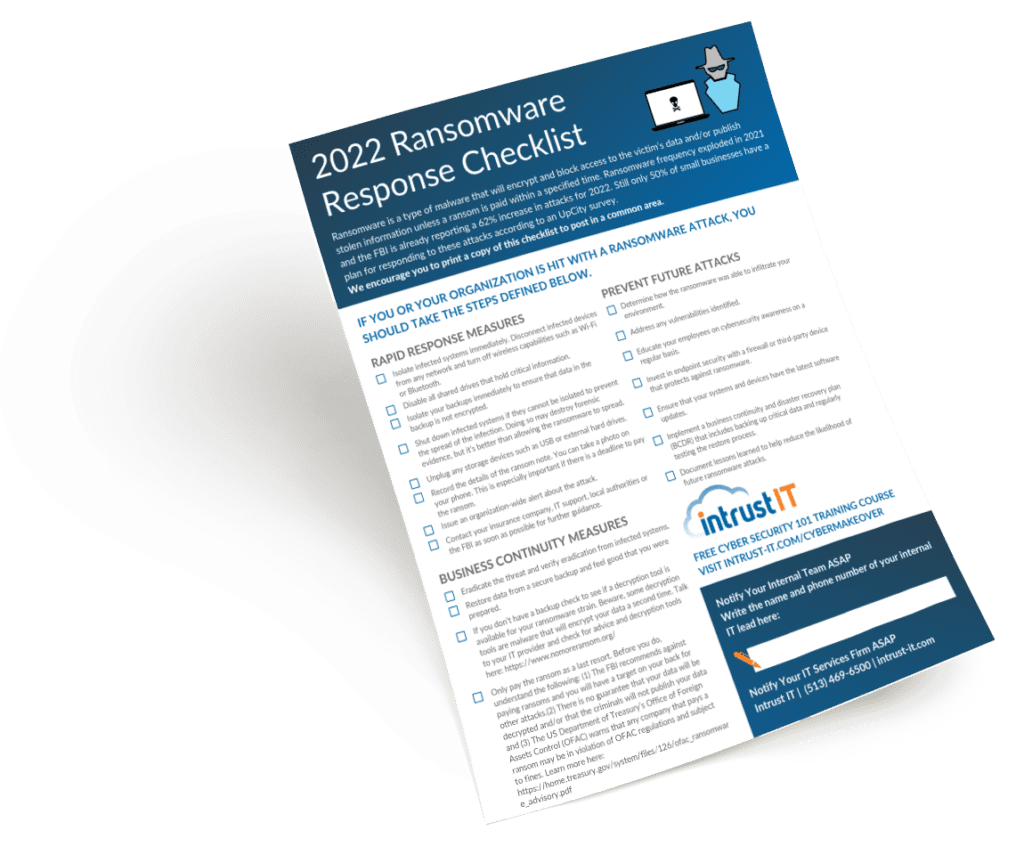
Downloadables (Checklists, Cheat Sheets & Guides)
Featured Videos
Explore the Latest Trends in IT
10 Signs It’s Time to Switch Providers
When it comes to managed IT support and supplemental IT services, there are a wide range of IT providers out...

Press Release: Intrust IT Acquires Managed IT Services Division from Afidence
Afidence Announces Sale of Managed IT Services Division to Intrust IT Afidence, a technology consulting and services firm headquartered in...
Microsoft Users Beware: What You Need To Know About the BazarCall Scam
Beware of the BazarCall ransomware scam, an elaborate new scam using a live call center to trick users of Windows...

Why Intrust IT Doesn’t Lock In Your Company, Has No Long-Term Contracts
One thing we despise at Intrust IT is long-term contracts. The business environment changes fast, so we need our vendors...
Request a SCAP Compliant Vulnerability Assessment
Our advanced, non-invasive internal and external scans can identify security, performance and stability issues in your network. Get a preliminary scan followed by in-depth consultation with our technical and compliance specialists. After some time to consider the findings, we'll run another round of scans and consultations before providing the final report.