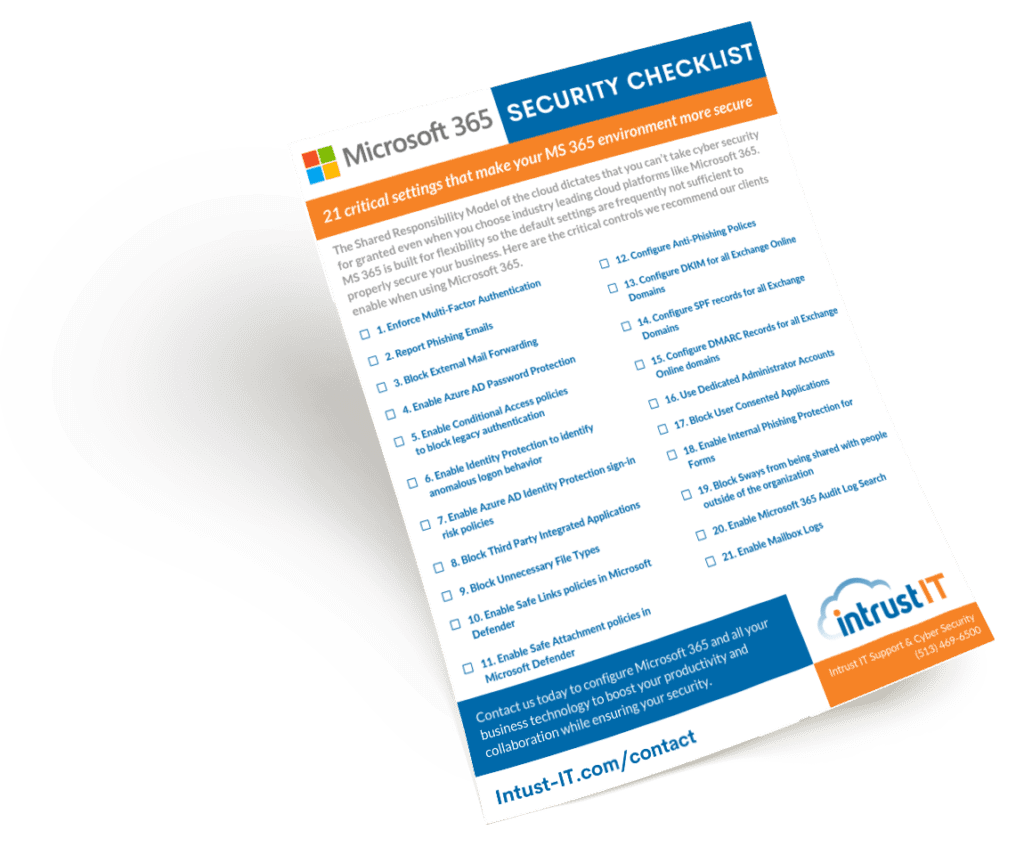
Downloadables (Checklists, Cheat Sheets & Guides)
Featured Videos
Explore the Latest Trends in IT

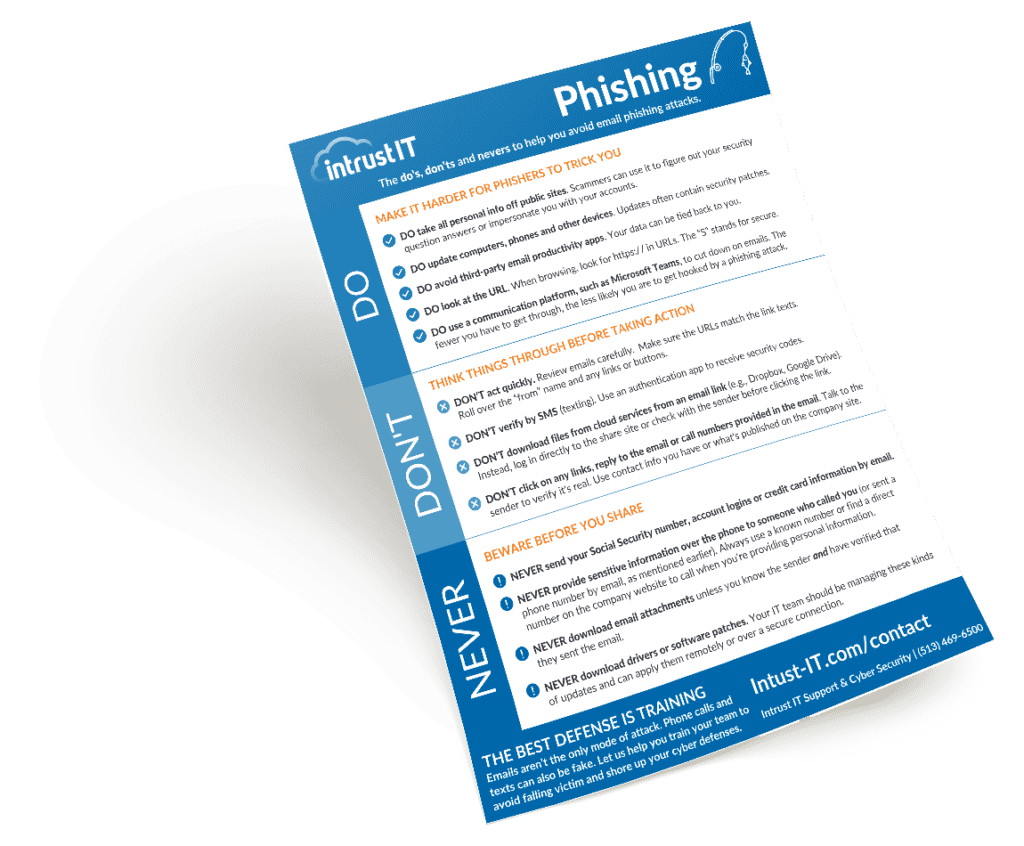
Phishing Email Kit: How to Spot and Avoid Them
Here's another watchout for your inbox: Scammers using a website to host a "phishing kit." Through the kit, scammers send...

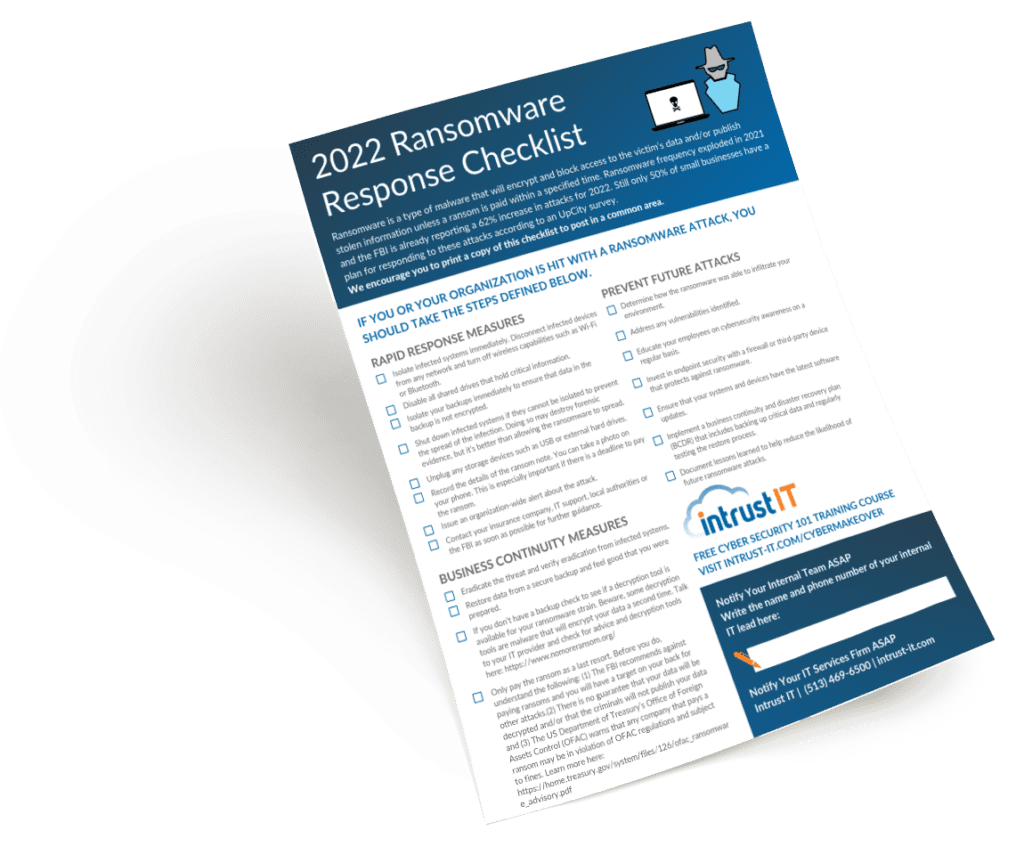
FBI Issues Russian Ransomware Attacks Warning: Is Your Business Protected?
Are you in position to protect your business from the threat of ransomware? Intrust, an IT managed services provider, can...

Crypto Mining on Company Servers
Here at Intrust IT, we've seen an increase in crypto mining on company servers with new and existing clients. Our...

Is Hiring IT Staff an Uphill Battle? You’re Not Alone
If you are finding that hiring IT staff feels impossible, you are not alone. According to a recent Wall Street...
Request a SCAP Compliant Vulnerability Assessment
Our advanced, non-invasive internal and external scans can identify security, performance and stability issues in your network. Get a preliminary scan followed by in-depth consultation with our technical and compliance specialists. After some time to consider the findings, we'll run another round of scans and consultations before providing the final report.